MS11-080 AfdJoinLeaf Privilege Escalation
Module Name
exploit/windows/local/ms11_080_afdjoinleaf
Authors
- Matteo Memelli
- Spencer McIntyre
References
Targets
- Automatic
- Windows XP SP2 / SP3
- Windows Server 2003 SP2
Platforms
- windows
Architectures
- x86
Reliability
Development
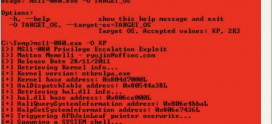
Module Options
To display the available options, load the module within the Metasploit console and run the commands ‘show options’ or ‘show advanced’:
msf > use exploit/windows/local/ms11_080_afdjoinleaf
msf exploit(ms11_080_afdjoinleaf) > show targets
...targets...
msf exploit(ms11_080_afdjoinleaf) > set TARGET <target-id>
msf exploit(ms11_080_afdjoinleaf) > show options
...show and set options...
msf exploit(ms11_080_afdjoinleaf) > exploit