Using Netcat To Spawn A Remote Shell
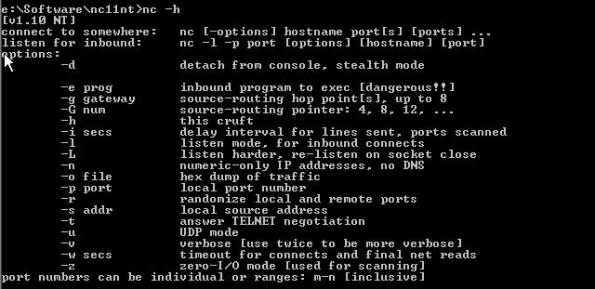
Introduction Netcat is one of those old school hacking tools that has been around for what seems like an eternity. Its stable release was made available back in March 20, 1996 and is currently available for download at http://netcat.sourceforge.net. That being said…I didn’t even get my first real computer until 1999, which was a Compaq Presario. […]
read more »